Threat Intelligence Report: react-icon-maker — npm Supply Chain Infostealer
Severity: Critical | Package: react-icon-maker v1.1.4 | Date: April 2026 | Author: Jordan Swebeck — Secure-ISS SOC
Executive Summary
A malicious npm package named react-icon-maker (version 1.1.4) has been identified
containing a fully functional infostealer payload. The package masquerades as a legitimate React
icon utility but delivers an AES-256-CBC encrypted JavaScript payload that exfiltrates browser
credentials, cryptocurrency wallet data, and macOS keychain files to a remote
command-and-control server.
Discovery
The package was identified through automated static analysis of npm packages as part of an
attack surface monitoring pipeline at Secure-ISS. The malicious logic was found in
dist/lib/default.js, which contained an encrypted data blob decrypted at runtime
using a hardcoded AES-256-CBC key and IV, with the resulting payload executed via
eval().
Technical Analysis
Delivery Mechanism
The malware uses a two-layer obfuscation approach:
- Layer 1 — AES Encryption: The primary payload is stored as a hex-encoded AES-256-CBC encrypted blob with a hardcoded key and IV embedded in the same file.
- Layer 2 — JavaScript Obfuscation: The decrypted payload is itself heavily obfuscated using control flow flattening, string array rotation, and custom base92 encoding — consistent with tools like obfuscator.io.
Execution chain:
default.js → decrypt AES blob → eval(obfuscated JS) → steal data → POST to C2
Hardcoded decryption parameters:
Key: 1aa9105f211ec5a6778c2643f5c9f271c5431253577da3c0b0cc3cb17c993eb3 IV: ab6233d8149cdac085ae296c4d57a833 Algorithm: AES-256-CBC
Capabilities
Credential Theft — targets browser login databases across all major browsers
on Windows, macOS, and Linux, hunting .ldb files and Login Data SQLite
databases from Chrome, Brave, Opera, Firefox, and Edge.
Cryptocurrency Wallet Exfiltration — over 20 browser-based crypto wallet
extensions targeted by extension ID, including MetaMask, Phantom, Coinbase Wallet, and Solflare.
Also directly targets Exodus desktop wallet files and Solana keypair files
(id.json).
macOS Keychain Harvesting — targets login.keychain and
browser-specific keychains under ~/Library/Keychains.
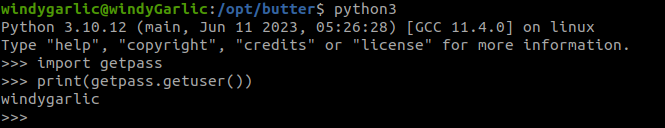
Second Stage Dropper — contacts a GitHub API endpoint to retrieve a module name, then downloads and executes a Python script from the C2 server for further post-exploitation.
Platform Awareness — separate execution paths for Windows, macOS, and Linux.
Indicators of Compromise
Network
| Type | Value |
|---|---|
| C2 IP | 45.61.128.61 |
| C2 Port | 1224 |
| Upload endpoint | http://45.61.128.61:1224/uploads |
| Payload download | http://45.61.128.61:1224/pdown |
File System
| Type | Value |
|---|---|
| Staging directory | ~/.n3/tp |
| Dropped archive (Windows) | %TEMP%\p5.zip |
| Python script drop | ~/.npl |
| Malicious file | dist/lib/default.js |
| Solana key target | ~/.config/solana/id.json |
| Exodus target (Linux) | ~/.config/Exodus/exodus.wallet |
| Exodus target (Windows) | AppData\Roaming\Exodus\exodus.wallet |
Package
| Type | Value |
|---|---|
| Package name | react-icon-maker |
| Malicious version | 1.1.4 |
| Registry | npmjs.com |
Targeted Wallet Extension IDs
| Extension ID | Wallet |
|---|---|
nkbihfbeogaeaoehlefnkodbefgpgknn | MetaMask |
ejbalbakoplchlghecdalmeeeajnim | Phantom |
fhbohimaelbohpjbbldcngcnapndodjp | Binance Chain Wallet |
hnfanknocfeofbddgcijnmhnfnkdnaad | Coinbase Wallet |
ibnejdfjmmkpcnlpebniachajginhoon | TronLink |
bfnaelmomeimhlpmgjnjophhpkkoljpa | Slope Wallet |
acmacodkjbdgmoleebolmdjonilkdbch | Solflare |
MITRE ATT&CK Mapping
| Technique ID | Name |
|---|---|
| T1195.001 | Supply Chain Compromise: Compromise Software Dependencies |
| T1027 | Obfuscated Files or Information |
| T1027.002 | Software Packing |
| T1059.007 | Command and Scripting Interpreter: JavaScript |
| T1555.003 | Credentials from Web Browsers |
| T1530 | Data from Cloud Storage Object |
| T1041 | Exfiltration Over C2 Channel |
| T1105 | Ingress Tool Transfer |
Recommended Actions
Immediate
- Block
45.61.128.61at perimeter firewall and proxy - Search npm audit logs and CI/CD pipelines for any installation of
react-icon-maker - Report the package to npm security at
security@npmjs.comfor takedown - Check endpoints for staging path
~/.n3/as a host compromise indicator
Investigative
- If the package was installed, treat the host as compromised — rotate all browser-stored credentials and crypto wallet private keys immediately
- Pivot on
45.61.128.61in VirusTotal, Shodan, and AbuseIPDB to identify related infrastructure and additional malicious packages from the same threat actor
Preventative
- Implement npm package allowlisting or integrity verification in CI/CD pipelines
- Consider tools such as Socket.dev for real-time malicious package detection
- Enforce least-privilege on developer workstations to limit the blast radius of credential theft malware
- Jordan Swebeck